A Multi Factor Authentication Quickstart
In the last couple of months, I started to dig deep into web security. I wanted to figure out, how the “dark side” works and how a hacker will act when he decided to penetrate my web application. So I downloaded a Kali Linux System, installed it on a virtual machine and started “hacking”…
I found some tutorials to hack and crack the neighbors Wifi and spy networks. Within two weekends, I was able to create Rainbow tables, using my GPU for decrypting passwords and also bought a new network adapter to collect more data. In summary I was able to do quite a lot without spending a huge amount of money or time.
This experience made me think about my personal security. If hacking is all about running a Kali Linux with an external Wifi Adapter in a Starbucks to observe the network traffic of all other customers around you and collecting all the passwords at the same time, it shouldn’t be that easy. Of course… hacking is not all about that, but it’s what most people understand about hacking. Nowadays you don’t need a lot of skills to grab some passwords in a network! So I was a little scared about my personal data and decided to secure myself a multi factor authentication!

That way of authentication wasn’t new to me, but I didn’t recognize the system behind it. Normally you log in with your username and password. A multi factor authentication adds new steps to your login!
For example:
To login into my github account, I just have to insert my username and my password. With more than one factor, I need to insert my username, my password and jump into my authenticator app on my smartphone to grab a on time pin! The combination of the username and password (something you know) and you one time pin on your phone (something you have) authenticate me into my account with two factors.
This is a little complicated? I don’t want to search my phone every time I login into my accounts. The reason, why you should use more factors are Man in the Middle (MitM) attacks and Keylogging. If you haven’t heard of it before, make sure you read this article about MitM Attacks in a nutshell. It doesn’t matter if someone knows your password, because it is always necessary to have something else to login!
Another reason is keylogging. Keylogger can be based on software or hardware. On Amazon, you can buy a hardware keylogger for less than 100€. Just put this little piece of hardware between the keyboard and the client and you are able to read everything what happens.
A multi factor authentication doesn’t need static passwords. So it doesn’t really matter what you type in into your keyboard, because you need your second device! I decided to buy a Yubikey, but any other device should be good as well. Even the touch Id on Apples iPhone is good for this purpose.
A Yubikey is one of the devices which are made for a multi factor authentication. I bought a Yubikey nano, which looks like a super small USB Stick. Other people won’t recognize that little stick in you usb slot, but the probability to loose it is pretty high of course. The Yubikey has two configuration slots.
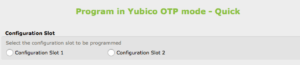
I used the first slot to create one time passwords (OTP). There are several web applications which support a Yubikey. For example: When I want to login into my Google Account, I have to insert my username and my password and I have to tap my little Yubikey to generate an OTP real quick.
The second configuration slot is used for a static password. This password was generated by my Yubikey itself, I don’t know it, but I use it as part of my master password! Before I am able to use my passwords in my password manager, I need to insert my master password. This is splitted into two areas as well. The first few letters are some I know, just like a normal password. The second part is my static password generated by my Yubikey which is the same all the time. To insert my static Yubikey password, I have to tap my Yubikey again for 3-4 seconds.
I also connected my Yubikey with my MacBook. The only way to login into my User is to insert the Yubikey into the Mac and insert my personal password (2 factors again).
To summarize:
The combination between a password manager, a second factor device, one time passwords and a two part master password makes me feel more safe.
You can’t be safe, but you can build a small fence for a potential hacker where he has to jump over first, before he starts lockpicking.
I asked myself, what will happen when I loose my Yubikey? The answer is easy… DON’T!!!!
Yubico recommends to have another Yubikey anywhere else in a secret place which is a duplicate of the original if you loose the first one. Just don’t loose it!
If you want to protect your web applications with a two factor authentication, you could use the libary from cmuench!
Let me know, what kinds of devices you use to protect yourself!